Crypto Ledger Security: Complete Architecture Analysis
Hardware protection, secure elements, and multi-layer defense for cryptocurrency safety.

Crypto Ledger Security represents a comprehensive approach to cryptocurrency protection that combines hardware isolation, certified secure elements, and multi-layer verification systems designed to protect digital assets against both digital and physical attack vectors. The security architecture fundamentally differs from software wallet approaches by isolating private keys inside specialized chips that resist extraction attempts even when attackers have physical access to the device. This hardware-first philosophy addresses the root vulnerabilities that have resulted in billions of dollars in cryptocurrency losses through software wallet compromises.
Crypto Ledger Wallet Security extends beyond simple key storage to encompass transaction verification, firmware integrity, device authenticity validation, and protection against sophisticated supply chain attacks. The architecture incorporates lessons learned from decades of banking security, smartcard technology, and dedicated cryptographic research. Unlike competitors like Trezor that use general-purpose microcontrollers, or KeepKey with different security models, Ledger devices employ CC EAL5+ certified secure elements specifically designed for cryptographic key protection. This page analyzes the security architecture, protection mechanisms, and verification standards that establish trust in the Crypto Ledger ecosystem.
Security Architecture Behind Crypto Ledger
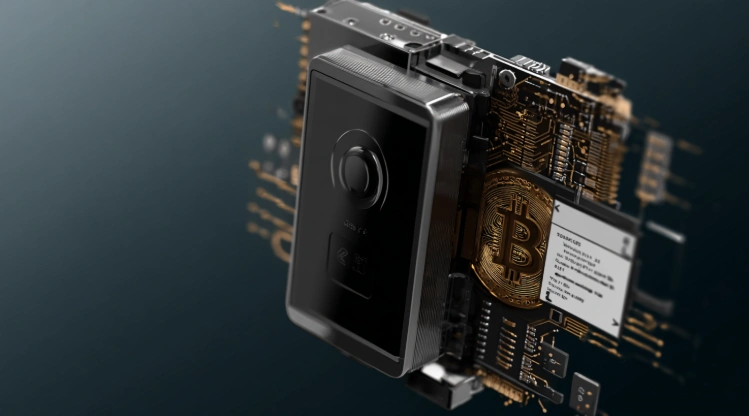
Crypto Ledger security architecture implements defense-in-depth principles through multiple independent protection layers working together to prevent unauthorized access to cryptocurrency holdings. The architecture separates security-critical operations from convenience features, ensuring that cryptographic functions occur exclusively within protected hardware environments while companion software handles user interface and network communication. This separation means that even complete compromise of the connected computer or smartphone cannot result in private key extraction.
Crypto Ledger wallet security operates through the principle of minimal trust, where each component assumes other components may be compromised and implements independent verification. The hardware wallet verifies firmware integrity before execution, the secure element validates commands before processing, and the display shows transaction details independent of potentially manipulated software. This approach creates multiple barriers that attackers must simultaneously overcome, dramatically increasing attack difficulty compared to single-layer protection models.
How Crypto Ledger Protects Digital Assets
Crypto Ledger protection operates through several distinct mechanisms working in concert:
- Secure element isolation prevents private key extraction through hardware barriers
- Independent display shows actual transaction details for user verification
- Physical confirmation requires button presses or touch for every signing operation
- Firmware verification ensures only authentic Ledger software executes
- Genuine check validates device authenticity against manufacturing records
- PIN protection prevents unauthorized device access after physical theft
- Recovery phrase enables asset restoration on replacement devices
Each mechanism addresses specific attack vectors identified through security research and real-world incidents affecting cryptocurrency users. The combination creates comprehensive protection exceeding any single security measure.
Hardware-Based Security Principles
Crypto Ledger hardware security follows established principles from banking and government security applications adapted for cryptocurrency protection:
| Security Principle | Implementation | Protection Provided |
|---|---|---|
| Key isolation | Secure element storage | Prevents remote key extraction |
| Minimal attack surface | Limited firmware functions | Reduces exploitation opportunities |
| Independent verification | Separate display hardware | Defeats screen manipulation attacks |
| Physical confirmation | Button/touch requirements | Blocks automated signing |
| Tamper resistance | Secure element design | Resists physical extraction attempts |
| Attestation | Genuine check process | Detects counterfeit devices |
Hardware security provides protection that software alone cannot achieve because the protective mechanisms exist in physical form rather than as code that could be modified or bypassed through software vulnerabilities.
Multi-Layer Defense System

Crypto Ledger security model implements multiple independent layers that must all be compromised for successful attacks. The layered approach means that vulnerability in any single component does not result in asset loss, providing resilience against both known and novel attack methods. This defense-in-depth strategy represents security best practices adapted from critical infrastructure protection to cryptocurrency management.
The multi-layer system addresses different attack categories through specialized countermeasures. Network-based attacks encounter the air gap created by hardware wallet isolation from direct internet connectivity. Software attacks targeting the companion application cannot access keys stored in the secure element. Physical attacks against the device face tamper-resistant hardware and PIN-based lockout. Social engineering attacks targeting users encounter verification requirements that expose manipulation attempts.
Physical and Digital Protection Layers
Crypto Ledger protection spans both physical and digital domains:
Physical protection layers:
- Secure element chip resists physical tampering and extraction attempts.
- Device casing provides visual tamper evidence through seal integrity.
- PIN lockout wipes device after three consecutive incorrect attempts.
- Button confirmation requires physical access for transaction approval.
- Recovery phrase backup enables restoration without compromising security.
- Geographic distribution of backups protects against localized disasters.
- Metal backup accessories resist fire, water, and environmental damage.
- Safe storage recommendations address physical security requirements.
Digital protection layers:
- Firmware signature verification blocks unauthorized code execution
- Genuine check validates device authenticity through cryptographic attestation
- Companion software verification through checksums and code signing
- Network isolation prevents direct internet access to key material
- Transaction display verification enables detection of manipulation
The combination addresses the full spectrum of threats facing cryptocurrency holders from casual opportunists to sophisticated state-level attackers.
Security Certifications and Audits

Crypto Ledger security model undergoes rigorous independent verification through internationally recognized certification programs and continuous security research. Third-party validation provides objective confirmation that security claims match implementation reality, distinguishing genuine protection from marketing assertions. The certification process involves extensive testing by specialized laboratories with expertise in cryptographic hardware evaluation.
Certification standards applied to Ledger devices include Common Criteria evaluations at EAL5+ levels, representing the highest practical certification for commercial security products. The secure element chips undergo separate certification processes validating their resistance to physical attacks, side-channel analysis, and fault injection attempts. Unlike Trezor devices using uncertified microcontrollers or KeepKey with different approaches, Ledger's certified secure elements provide independently verified protection.
Third-Party Verification Standards
Crypto Ledger security undergoes multiple verification approaches:
- Common Criteria CC EAL5+ certification for secure element components
- ANSSI certification from French national cybersecurity agency
- Independent security audits by specialized cryptocurrency security firms
- Bug bounty programs incentivizing responsible vulnerability disclosure
- Open-source firmware enabling community security review
- Academic research collaboration advancing hardware wallet security
The combination of certification, audit, and community review creates comprehensive verification that identifies and addresses vulnerabilities before attackers can exploit them. Ongoing programs ensure security keeps pace with evolving threats rather than remaining static after initial product launch.
For private key protection, see our Crypto Ledger Private Keys guide. For phishing protection, visit Crypto Ledger Phishing Protection. For safety analysis, see Is Crypto Ledger Safe.
Frequently Asked Questions
Hardware isolation keeps private keys inside certified secure elements that resist extraction. Software wallets store keys on general-purpose devices vulnerable to malware, keyloggers, and remote attacks.
The secure element protecting private keys has not been successfully attacked. A 2020 customer database breach exposed personal information but did not affect cryptocurrency security or wallet protection.
Ledger uses CC EAL5+ certified secure elements while Trezor uses general-purpose microcontrollers. Both provide significantly better security than software wallets with different architectural approaches.
No security is absolute. Ledger protects against remote attacks, malware, and most physical attacks but cannot prevent users from voluntarily revealing recovery phrases through social engineering.
Encryption protects data at rest but keys must be decrypted for use, creating vulnerability windows. Hardware security keeps keys permanently protected inside secure elements that sign transactions without key exposure.
Independent certification validates security claims through rigorous testing. Users can trust certified security rather than relying solely on manufacturer assertions that may not reflect actual protection.
All current devices use identical ST33K1M5 secure elements with equivalent cryptographic protection. Price differences reflect screen, connectivity, and form factor rather than security level.